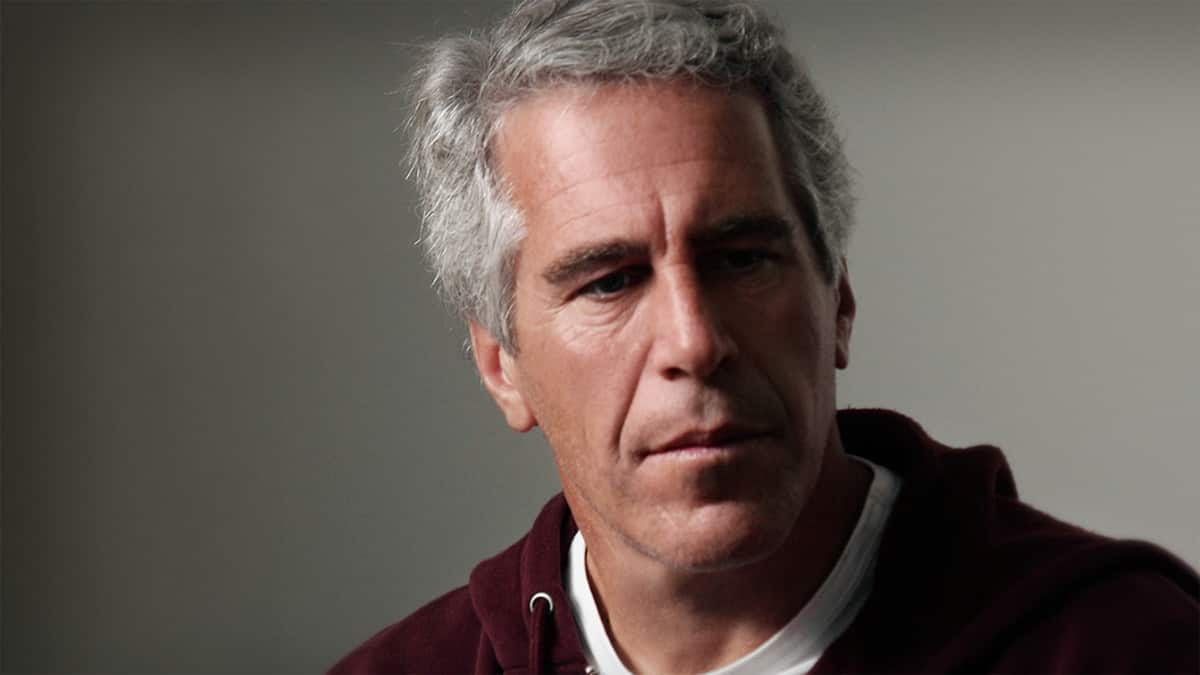
The intersection of private aviation and sovereign military infrastructure represents a critical failure in jurisdictional oversight. When non-military aircraft utilize Ministry of Defence (MoD) assets, they bypass the standard scrutiny of civilian Border Force protocols, creating a "grey zone" of accountability. The current investigation into Jeffrey Epstein’s alleged use of British military airbases—specifically RAF Northolt and potentially RAF Mildenhall—is not merely a scandal of association; it is a case study in the breakdown of military-civilian operational boundaries. Understanding how a private individual could leverage state-funded strategic hubs requires a deconstruction of the United Kingdom’s Visiting Forces Act and the specific "Indemnity and Billing" frameworks that govern non-departmental flights.
The Architecture of the Oversight Gap
Private aircraft do not land at military installations by accident. The process requires a rigorous sequence of clearances, often involving the "Special Flights" desk or direct diplomatic sponsorship. To evaluate how Epstein’s aircraft may have integrated into this system, we must examine the three primary mechanisms of access. If you liked this article, you should check out: this related article.
1. The Diplomatic Clearance (DIPCLEAR) Vector
The most common route for non-military aircraft to access RAF bases is through a DIPCLEAR. This is usually reserved for foreign heads of state, high-ranking government officials, or those traveling on behalf of a sovereign entity. If Epstein’s Gulfstream was categorized under a "Mission" status—perhaps through his extensive network of political and royal contacts—the standard manifests would be subject to reduced scrutiny. The failure here is one of Categorization Bias, where the status of the passenger overrides the security vetting of the aircraft's intent.
2. Operational Diversion and Alternate Landing Sites (ALS)
RAF Northolt, located in West London, serves as the primary hub for the 32 (The Royal) Squadron. It operates under different noise and time constraints than Heathrow or Northolt’s civilian counterparts like Farnborough. For a high-net-worth individual, a military base offers two strategic advantages: For another angle on this development, see the latest update from The New York Times.
- Discretionary Shielding: Military bases are exempt from the Freedom of Information Act (FOIA) requests that apply to civilian airport logs in the same granular detail.
- Physical Security: The perimeter of an RAF base is guarded by armed military personnel, providing a level of privacy and exclusion that even the most elite private terminals (FBOs) cannot guarantee.
3. The "Service Provision" Loophole
The MoD often recoups costs by allowing commercial or private entities to use underutilized runway capacity under specific "Joint Use" agreements. These agreements are governed by the Military Aviation Authority (MAA). If Epstein’s movements were logged as "business-related support" for a military contractor or a visiting dignitary, the flight would enter the system as a "Special Usage" event.
Quantifying the Accountability Deficit
The core issue in the UK Defence Ministry’s probe is the Data Persistence Problem. Unlike civilian flight trackers (such as ADS-B Exchange or FlightAware), military transponder data is often masked or filtered for national security reasons.
Data Silos and Manifest Integrity
The investigation faces a bottleneck in the reconciliation of two distinct data sets:
- The Global Movement Log: Which tracks the physical airframe via tail number.
- The Passenger Manifest (Form F-104 equivalent): Which identifies the individuals on board.
In a civilian environment, these are synchronized by Border Force. On a military base, the RAF Police or the base security detachment handles the arrival. If the aircraft was handled as a "VIP transit," the passengers may have been escorted directly from the tarmac to a secure vehicle without passing through a centralized immigration hall. This creates a Data Black Hole, where the aircraft's presence is recorded, but the cargo—human or otherwise—remains unverified.
The Cost Function of Sovereign Immunity
The use of military bases by private citizens incurs a hidden cost to state legitimacy. This can be modeled as an Institutional Trust Decay Function. When a sovereign asset is used to facilitate the movement of an individual engaged in transnational criminal activity, the "Negative Externality" is the erosion of the military’s perceived neutrality.
- Variable A (Strategic Asset): The base itself (e.g., RAF Northolt).
- Variable B (Access Cost): The nominal fee paid for landing.
- Variable C (Reputational Risk): The fallout from the investigation.
The current probe must determine if Variable B was significantly lower than the market rate, suggesting "soft corruption" or undue influence. Furthermore, the investigation must identify the Sponsoring Authority. A private aircraft cannot land at an RAF base without an internal "Owner"—a person or department within the MoD or the Foreign, Commonwealth & Development Office (FCDO) who vouches for the flight.
Logistical Anomalies in the Epstein Flight Patterns
Analysis of known flight data suggests that Epstein’s movements often favored "Pathways of Least Resistance." If the investigation confirms the use of RAF assets, it would indicate a deliberate strategy to circumvent the Common Travel Area (CTA) monitoring systems.
The structural advantage of a military base is the Exemption from Routine Customs. While military personnel are subject to strict rules, "VIP guests" often receive expedited processing. This is not a failure of the rules, but a failure of the Discretionary Power granted to base commanders. If a base commander receives a call from a high-ranking official stating that a "friend of the Crown" or a "strategic partner" is arriving, the standard operating procedure (SOP) is often bypassed in favor of "Tactical Courtesy."
The Burden of Retroactive Audit
The Ministry of Defence faces a significant technical challenge in its probe: Hardware Obsolescence. Flight logs from the early 2000s may exist only in paper format or in legacy databases that are not indexed for search. To conduct a "masterclass" analysis of these movements, the MoD must deploy a multi-vector audit:
- ATC Tape Analysis: Recovering recorded communications between the aircraft and the tower to identify the callsign used. Use of a non-standard callsign would indicate a high level of coordination.
- Fuel Requisition Records: Cross-referencing fuel purchases. Private aircraft must pay for fuel, often via a specialized military-to-civilian billing bridge. These financial records are harder to erase than flight manifests.
- Ground Handling Logs: Identifying which private contractors (if any) were brought onto the base to service the aircraft.
Structural Recommendations for Military-Civilian Interoperability
The Epstein case reveals a systemic vulnerability in how Western militaries manage non-combatant assets. To mitigate this risk, the following structural changes are required:
- Mandatory Civilian Mirroring: Every non-military flight landing at a military installation must have a mirrored entry in the civilian Border Force "Global Passenger Tracking" system, regardless of the passenger’s status.
- Audit of Sponsoring Identities: The "Sponsoring Authority" for any private flight must be recorded in a permanent, non-editable blockchain-style ledger to ensure future accountability.
- The "High-Risk" Filter: Automated flags for aircraft registered in offshore jurisdictions (e.g., the US Virgin Islands, where Epstein’s aircraft were often registered) should trigger mandatory, non-discretionary inspections.
The failure to monitor these "grey flights" is a failure of Systems Architecture. By allowing a private individual to co-opt the prestige and security of the Royal Air Force, the state provided a "Sovereign Cloak" for activities that would have otherwise triggered civilian law enforcement alarms.
The investigation’s ultimate success will not be measured by the confirmation of a single landing, but by the exposure of the influence network that facilitated it. The military must move away from a "Trust-Based" VIP model to a "Verification-Based" operational model. This requires the immediate decommissioning of discretionary landing rights for non-state actors unless they are on a documented, audited mission of national importance. The era of "Tactical Courtesy" must end to preserve the integrity of the strategic infrastructure.
The strategic play here is a complete decoupling of "VIP status" from "Security Clearance." The MoD should immediately implement a "Digital Border" within its airbases that operates independently of the chain of command, ensuring that the identity of every passenger on a private airframe is logged by an external agency, removing the possibility of localized suppression of data. This is the only way to prevent the state from becoming an unwitting accomplice to the "Logistics of Impunity."